As today’s cyber threat landscape grows ever more dangerous, federal officials are looking to zero trust for answers to their toughest cybersecurity vulnerabilities. The zero trust model operates on a foundation of “trust nothing, verify everything,” and today, organizations are moving away from the castle-and-moat approach to security and instead gravitating toward a perimeterless model that relies on constant authentication and verification of a user’s identity and credentials.
However, as agencies move forward with the approach, officials warn that zero trust shouldn’t be treated as a singular solution, but instead as an overarching, holistic method that fits into existing IT architecture while having the flexibility to integrate future technologies and advancements.
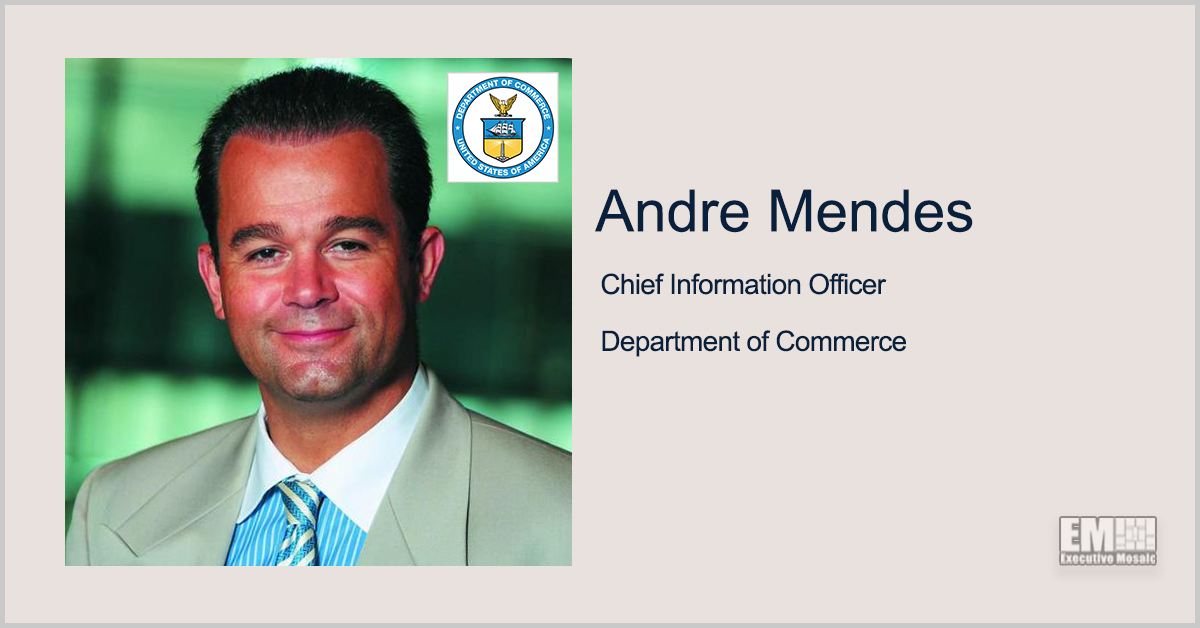
Andre Mendes, chief information officer for the Department of Commerce, described zero trust as “an evolution — a journey, more than a system that you can deploy.”
“It’s composed of a lot of interplay between the various parts of your entire technical landscape,” Mendes said in his keynote address at the Implementing Proactive Security With Zero Trust Forum hosted by GovCon Wire Events.
This interplay, Mendes explained, is a critical component of implementing a zero trust architecture that is resilient, adaptable and reliable.
“Across your entire technology stack, it’s extremely important to create a modularity based on interfaces that are standard, so that at any point of the equation, you can remove a component and plug in another component that operates seamlessly both up and down the technology stack and continues to allow you to move forward,” he said.
Evolutionary pressures — on employees, vendors, policies, organizations and more — will continue to drive advancements for cybersecurity. Zero trust architecture is just the latest evolution of security, Mendes noted, and as paradigms continue to shift, so will zero trust.
Currently, a crucial component of zero trust is ICAM, or identity, credential and access management. ICAM frameworks allow organizations to to ensure that critical information, data and systems are being accessed by the right users at the right time and for the right reasons.
In his keynote address, Mendes predicted that in the future, these ICAM clearance procedures and checkpoints will be able to operate at near real-time. Much like the credit scoring system, Mendes foresees a clearance scoring system on the horizon in the public sector.
He suggested that with the future of zero trust architecture, “what you’re going to be looking at is a clearance score for access, control, grant or revocation that might change on a constant basis based on a variety of factors.”
“It will effectively give individuals or organizations some degree of control over what is one of the biggest threats from a cybersecurity standpoint, which is the internal threat,” he anticipated.
Join GovCon Wire for its next event, the Second Annual Defense and Intelligence: IT Modernization Forum on Sep. 6 to hear from leaders across the public and private sectors as they discuss how the intelligence and defense communities intersect to protect our nation against an evolving threat.
CIA Chief Information Officer La’Naia Jones is scheduled to keynote. Click here to register.