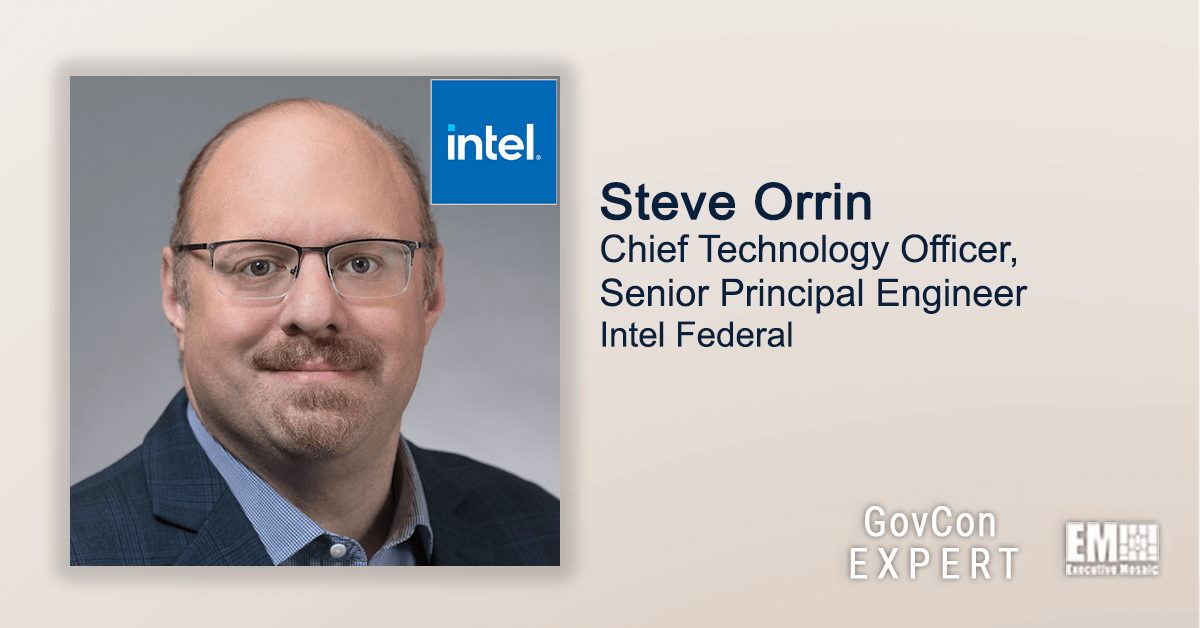
Steve Orrin, chief technology officer and senior principal engineer at Intel Federal, published the second part of his first featured article as a member of Executive Mosaic’s GovCon Expert program on Wednesday.
GovCon Expert Steve Orrin provides an insightful look into the current cybersecurity space as federal agencies work to address the challenges of zero-trust implementation and the new set of standards of the current administration’s cybersecurity guidance.
In part two of his first feature, Orrin discussed the lack of information from the current administration on implementing the guidelines and set of standards of IT vendors as well as the providers of hardware and software services.
You can read Steve Orrin’s full GovCon Expert article below:
President’s Warning on Cyberattacks, Part 2: How IT Vendors Should Implement the Guidance
By Steve Orrin
On March 21, President Biden issued a statement warning of imminent cyberattacks, backed by the Russian government, against the U.S. public and private sectors. The statement pointed to a White House factsheet that offers guidance on how both enterprises and technology providers can prepare for such attacks.
While the guidance offers sound high-level advice for shoring up cybersecurity, it provides little practical details on how organizations can implement the safeguards. Part 1 of this two-part series described strategies for implementing the eight recommendations for enterprises. Part 2 explores best practices for the five recommendations for providers of hardware, software and IT services.
1. Build security into technology products from the ground up.
An unsecured digital product or tool becomes the weak link in a chain that affects every digital product or tool. The IT industry can no longer simply rely on cybersecurity providers to protect against vulnerabilities and attacks. Instead, every vendor must take responsibility for cybersecurity.
That means security must be part of every product’s DNA from square one. That starts at the requirements phase and continues through design, coding, manufacture and ongoing enhancements. It’s simply too complex and ineffective to try to bolt-on security later. And security can’t just be part of DevSecOps for software development. It also needs to be baked into hardware, firmware, tools, libraries, open-source and so on.
2. Develop software only on highly secure infrastructure.
Recent years have seen high-profile attacks on the IT supply chain. The lesson is that we need to better secure our development processes and infrastructure. In particular, the systems and networks that support development must be segmented from corporate networks. Just as industrial systems are isolated from operational systems, so development infrastructure must be isolated. That’s simply treating development like the critical asset it is.
Of course, it’s difficult to air-gap your developers, because they have to access corporate systems like any other employees. The solution is virtual segmentation to protect development infrastructure throughout the development lifecycle, from design to repositories, testing and build. The goal is to prevent attackers that breakthrough one door from opening another door on your organization’s intellectual property. You can achieve that goal through network segmentation, strong authentication and data access controls.
3. Leverage automation to check for vulnerabilities.
Just as enterprises deploying software should automate patch testing, IT vendors need to automate proactive vulnerability testing. A wealth of automation, source-code analysis and quality-assessment tools is available. The key is to integrate them into your processes so that as you create software, you’re testing and validating to ensure security is built in from the ground up.
A related strategy is to create a security foundation library. If you require developers to build or download the security features they need, you end up with a highly heterogeneous environment. Instead, establish a set of foundational tools, techniques and objects they can leverage to implement security features. These include login functions, data- and input-validation functions, crypto functions and secure network access protocols. That way, developers are using a common base to build security into your products.
4. Take responsibility for all code used in your products.
Software no longer involves only code created by the software vendor. It also incorporates code created by others. IT providers need to take responsibility for the security of all code in their products – whether it’s built by internal developers, supplied by external coders, downloaded from open source or licensed from a third party.
New techniques, like a software bill of materials (SBOM) and Google’s Supply-chain Levels for Software Artifacts (SLSA), are mechanisms that provide visibility into what’s actually in software. Vendors should adopt these mechanisms to make transparent to customers what’s in the box.
That way, as customers build out complex hardware and software ecosystems, they can track the security of products over time. Whenever a third-party or open-source module becomes vulnerable to attack, customers can refer to their library of BOMs to quickly see which products are affected. This approach will enable the IT industry and the customers it serves to better manage cyber risk.
5. Implement zero-trust security.
All the recommendations provided here are foundational technologies, processes and best practices that help move the IT industry toward a zero-trust framework. After all, zero trust isn’t a cybersecurity solution or even a portfolio of solutions. Rather, it’s a mindset and methodology for applying security policies, processes and technologies, from end users to software deployment to everyday data access.
Zero trust needs to be implemented in a way that incorporates continuous monitoring, continuous authentication, limited access, “deny by default,” and so on. These are all enabled by having foundational security capabilities and process build in, from design to deployment to production.
How will we achieve the goals of zero trust? Collectively, as an industry. We need to build in cybersecurity from square one. We need to implement better processes around how we ensure security. And we must enable customers to make better risk determinations around the use of the hardware, software and IT services we deliver.
About GovCon Expert Steve Orrin
Steve Orrin is Intel’s Federal CTO and a Senior Principal Engineer. He leads Public Sector Solution Architecture, Strategy, and Technology Engagements and has held technology leadership positions at Intel where he has led cybersecurity programs, products, and strategy.
Steve was previously CSO for Sarvega, CTO of Sanctum, CTO and co-founder of LockStar, and CTO at SynData Technologies. Steve is a recognized expert and frequent lecturer on enterprise security.
He was named one of InfoWorld’s Top 25 CTO’s, received Executive Mosaic’s Top CTO Executives Award, was the Vice-Chair of the NSITC/IDESG Security Committee and was a Guest Researcher at NIST’s National Cybersecurity Center of Excellence (NCCoE).
He is a fellow at the Center for Advanced Defense Studies and the vice-chair of the INSA Cyber Committee.