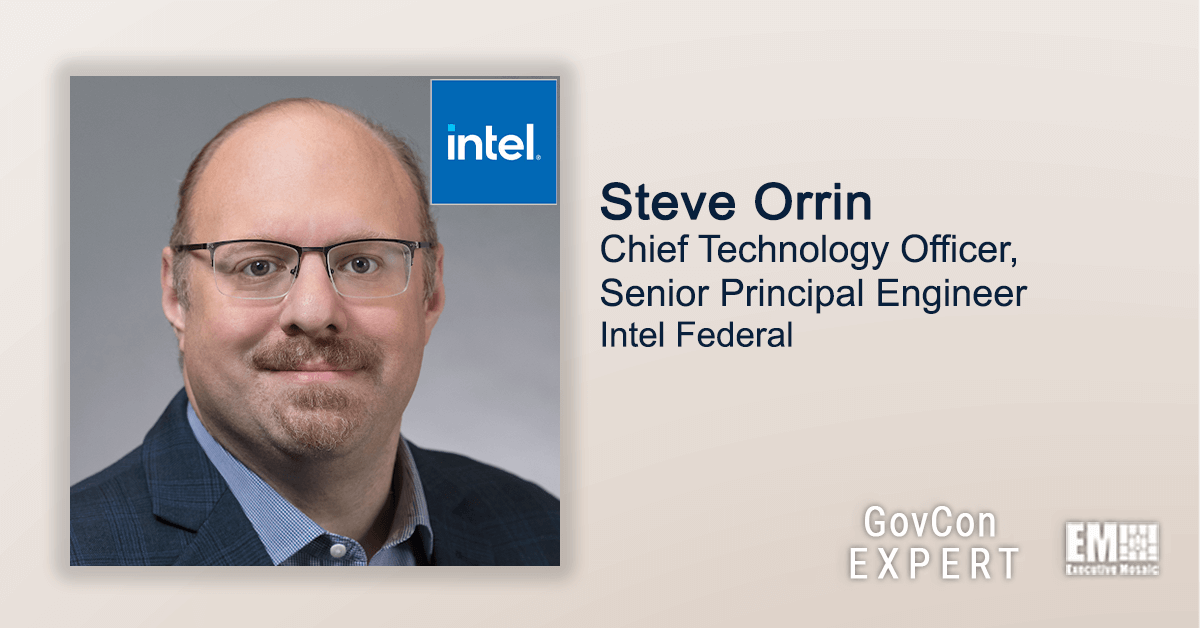
GovCon Expert Steve Orrin, chief technology officer and senior principal engineer at Intel Federal, recently spoke with GovCon Wire regarding the challenges that government agencies and federal organizations are facing to implement zero-trust architectures and refocus their data security.
In addition, GovCon Expert Steve Orrin also discussed the values that Intel Federal looks for in its workforce as well as how they approach recruitment in the federal landscape and a lot more during the latest Executive Spotlight interview.
“The federal government and industry are both looking at game-changing technologies and trying to see how they will impact the business as well as the operations in the enterprise.
One of the areas where the government is doing very well is thinking bigger than any one technology. It’s not about 5G, AI, cloud or any other one technology. It’s the mechanism and methods to implement them. It’s about people and the mission.”
You can read the full interview with GovCon Expert Steve Orrin below:
GovCon Wire: What do you see as the most critical challenges facing those in the federal sector as cybersecurity continues to rise in importance and cyber hygiene becomes a necessity for all companies and even more critical at the national security level?
Steve Orrin: “At Intel, we are working hard to help customers keep pace with today’s cybersecurity challenges and evolving threat landscape, particularly the prolonged remote work model and dramatic increase in ransomware activity.
In the face of heightened cyber risk in the federal sector, it’s important to start with proper cyber hygiene, having a plan in place for resiliency/recovery, and deploying cybersecurity controls beyond the four walls of an agency.
As the perimeter expands, data can’t be constrained by a particular firewall or even physical boundaries. There is no “hard shell” anymore – security controls must reside with the data. Cyber hygiene is especially important in light of federal policy changes.
For instance, we are helping our clients step up their security policy and practices to support new mandates such as The White House’s Memorandum on Improving the Nation’s Cybersecurity, particularly around efforts to enhance supply chain security and adopt a zero-trust approach to security.
One of the big takeaways that we’ve learned over these past months is that, because the environment is always changing, no one is immune to the latest ransomware or data breaches. Any aspect of a federal agency’s digital infrastructure could be a target and must have appropriate security controls. That’s one of the reasons why zero-trust made it into the memorandum.
Another significant challenge that the federal government must address is the increased workload that its workforce is experiencing due to these process and procedural changes – as well as the wider talent issues in the federal sector.
To overcome these challenges, we believe that the federal government and industry must think differently about cybersecurity and move forward with a solution-based approach that considers the entire enterprise – on-premises and off – and ensures secure access to digital assets and enforce the right security controls.”
GovCon Wire: How does Intel Federal ensure long-term success for your workforce to drive value for your employees as you continue to face the uphill challenge to recruit and retain the best talent in the federal marketplace?
Steve Orrin: “Cybersecurity talent has been a challenge across the board – for the federal government and industry. In the federal space, hiring and retaining talent isn’t easy. Agencies are also dealing with the reality that sometimes ‘the grass looks greener on the other side’ and security teams are leaving government for the private sector.
An innovative approach to this problem is to allow cyber talent to spend time in both worlds. The government is exposed to unique and persistent threats and the work and sense of mission is often more meaningful than jobs in private enterprise.
It’s also a great place for on-the-job training, particularly for college graduates who also bring fresh perspectives to today’s challenges. In turn, these positions can open doors to lucrative jobs in industry where that same skillset can be further developed and, as we do here at Intel Federal, provide opportunities to continue to serve and protect federal missions.
So we encourage our employees and anyone wishing to enter the field to play with the technology and seek new opportunities. Cyber is a recession-proof industry. There will always be a need for talented people in cybersecurity.
The key is to help create the right environments for talented people to learn and hone their skills – in the government, industry, or academia. Over time, the workforce will begin to catch up and we’ll see what the future holds.”
GovCon Wire: With zero-trust technology becoming a major focal point moving forward, what can you tell us about the difficulties of implementing zero-trust architectures and focusing on data security?
Steve Orrin: “The first thing to recognize is that zero-trust is an approach. It’s not a product or a piece of technology that you can plug and play. There’s no silver bullet. A lot of people are under the impression that zero-trust means going back to zero and throwing away everything you’ve done before. That couldn’t be further from the truth.
Zero-trust builds off defense-in-depth and risk-based approaches to security but takes us to the next level. As soon as a user logs onto their VPN, they have access to all any number of data and applications. They are through the door. What zero-trust does is say that the authentication and validation shouldn’t stop there; trust assertions should continue.
Agencies must continuously authenticate. That doesn’t mean users have to enter their password or use two-factor authentication every 10 minutes. What it means is that agencies must deploy policies and monitoring systems that validate that the user still has the right to access that information – in real-time.
Zero-trust is essentially about tying risk security mechanisms that form part of an agency’s broader cybersecurity framework and making them actionable using continuous monitoring. In this way, zero-trust is not just about the network.
It’s about the data and where it flows. It’s about the resources and services they agency is providing. Those are not necessarily bound to a specific network or domain. For instance, an agency’s edge system could be disconnected from the network, yet access must still be controlled using strong authentication and monitored continuously.
To establish trust and ensure rapid real-time response, agencies must build off a foundation of cybersecurity best practice and make it actionable, continuous, and validated. It’s an approach that will make a big difference in how we all move forward to combat our nation’s critical cybersecurity challenges.”