It’s a cliché at this point to say the government moves slowly in terms of technology modernization and procurement of new tools and services. However, sometimes societal occurrences and world events come knocking and shake bureaucracy out of its glacial processes, forcing the federal sector to act sooner and faster.
The combined effects of major cybercriminal activities like the 2020 SolarWinds hack and the 2021 Colonial Pipeline ransomware incident along with the electronic warfare-saturated events of the Russian invasion of Ukraine have been “galvanizing” and “put a fine point” on the need for the government to act swiftly on cybersecurity matters, according to Federal Chief Information Security Officer Chris DeRusha.
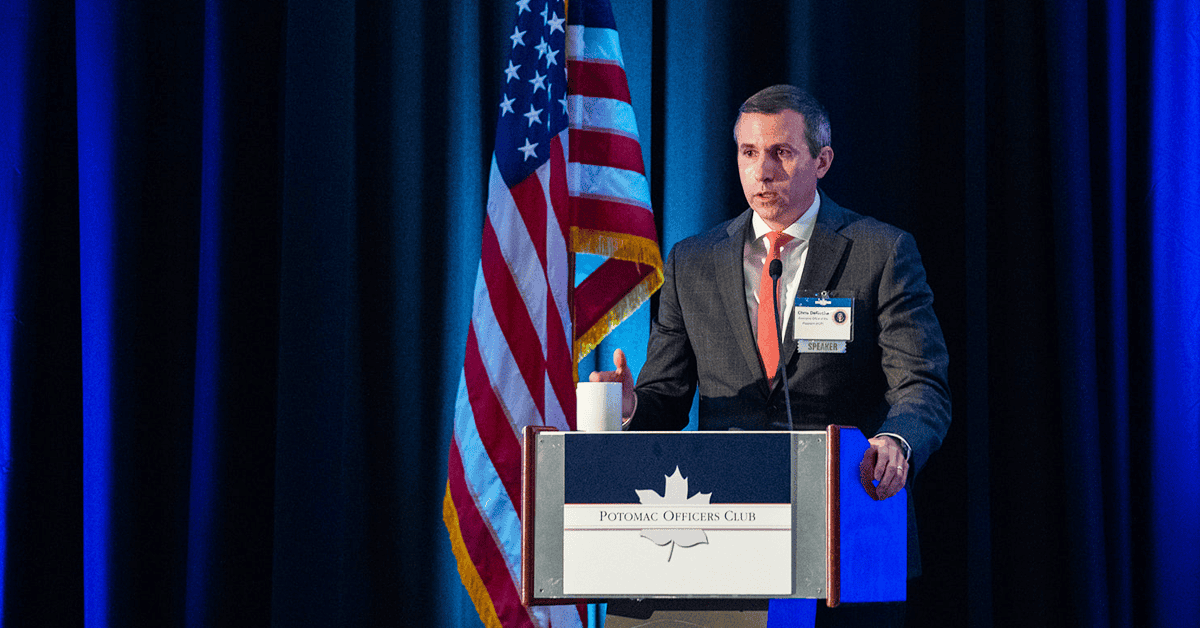
“We’ve got more momentum than I’ve seen [before],” DeRusha told an audience member at the Potomac Officers Club’s 2023 Cyber Summit on Thursday. The questioner was inquiring why there are still major incursions on sensitive data, such as a February intrusion into U.S. Marshals systems and mentioned that the FBI was “still not completing a lot of the basic [Continuous Diagnostic and Mitigation] things.” DeRusha’s answer, and his preceding remarks during his keynote speech, were an assurance that the Biden administration is working hard to build up effective defenses against such attacks.
DeRusha, a past Wash100 Award winner, said that it is rare to have the President’s full support on a project as the federal cyber community does, given the National Cybersecurity Strategy that was released by the administration in March.
“It’s trying to chart out an optimistic future,” DeRusha said of the strategy. “I think that’s important. We have to believe that we can handle these risks and that we can solve these problems. We all know how hard it is, but we have to have an optimistic outlook and a plan for becoming more defensible and resilient.”
The Executive Office CISO, who is also deputy national cyber director, went on to reason that it’s unrealistic to think the government is going to stop every behavior from a cyber bad actor, but he said the goal of the recently released strategy, and the next decade of cyber policies, is to “reduce the noise down to a point where we can manage it and prioritize these risks.”
Defending critical infrastructure, harmonizing regulations, disrupting and dismantling threat actors and forging partnerships are among the main tenets of the Cybersecurity Strategy, DeRusha explained. He also said the Office of the President debated whether or not to write a separate federally-focused strategy, but instead folded it into the larger national guidelines. Key to the federal side of things is developing an operational model that dictates what service lines agencies need from the Cybersecurity and Infrastructure Security Agency and creating alignment across the “big three environments,” a.k.a., federal civilian and the defense and intelligence communities, with whom the President’s office works “hand in glove.”
DeRusha spoke to the need for a “public-facing implementation plan” to accompany the strategy, which he said was something the Obama administration lacked during his time working at the White House nearly a decade ago. He told onlookers at the POC summit that this plan would be published sometime this summer.
Finally, the White House CISO addressed the audience of primarily commercial sector government contracting professionals directly, saying that the “resourced community” of “critical infrastructure owners and operators, big tech companies and government” “has to do more” in order for data and intelligence to be protected on a national scale.
“We have to do as much as we possibly can to provision and secure technology, products, services. We cannot have this, sort of, ‘deliberate defaults, no password, bad passwords. Here’s a cloud environment; you can put in security if you’d like.’ It’s not working. Because…it’s putting it on the least resourced, the least knowledgeable, to somehow figure out what they’re supposed to and that is not working,” DeRusha emphasized.