Mick Fox, chief operating officer for Technomile, published his latest feature article as a member of Executive Mosaic’s GovCon Expert program on Thursday.
Previously, GovCon Expert Mick Fox provided an informative guide in a two-part feature breaking down contract lifecycle management (CLM) in the federal landscape today.
For his latest piece, Fox discussed the need to understand FedRAMP considerations and how they impact Cloud-based CLM solutions, SaaS evaluations and more.
Visit GovConWire.com to read the latest features on our industry from the most significant executives of consequence in the GovCon industry and federal sector. Become a GovCon Expert today!
You can read Mick Fox’s next GovCon Expert article below:
Three Things a Contracts Professional Must Consider Regarding FedRAMP
By Technomile COO Mick Fox
As a contract professional at an Aerospace & Defense company who may be charged with researching and evaluating Contract Lifecycle Management (CLM) software for your organization, working knowledge of FedRAMP considerations is critical.
Yes, no doubt your IT business partners will help you vet this in grave detail as you proceed deeper into your CLM selection process, but my goal with this article is to empower you to immediately home in on CLM vendors that can successfully support your FedRAMP compliance requirements – why waste time considering vendors that cannot?
First, a quick FedRAMP refresher. As explained on FedRAMP.gov, “The Federal Risk and Authorization Management Program (FedRAMP) was established in 2011 to provide a cost-effective, risk-based approach for the adoption and use of cloud services by the federal government.”
FedRAMP sets forward the requirements that apply to all federal agencies when federal information is collected, maintained, processed, disseminated, or disposed of by Cloud Service Providers (CSPs).
Federal agencies must ensure FedRAMP requirements are met, as well as hold their contractors accountable by including FedRAMP requirements in performance criteria and deliverables included in contract awards.
In a nutshell, your potential new CLM solution will house federal information, so it is vital to consider FedRAMP in your evaluation of any cloud-based CLM solution in order to ensure your company’s compliance obligations are met. Here are three key considerations:
Cloud-based CLM solutions come in two key flavors, each with unique approaches to FedRAMP
As you explore the CLM software market, you’ll find there are two key models for cloud-based CLM solutions: Software as a Service (SaaS) and natively-built cloud applications. Let’s look at each one and the corresponding FedRAMP implications:
SaaS – With this model, the CLM vendor itself is considered a CSP, supplying not only the web-based CLM software, but also the underlying infrastructure and platform-layer controls. This makes the vendor and their CLM product eligible to pursue and obtain FedRAMP authorization.
Natively-Built Cloud Applications – In contrast to the approach above, an Independent Software Vendor (ISV) natively builds and deploys its CLM software on a third-party’s platform, such as Microsoft Dynamics 365, Salesforce, or others (think software available in these platforms’ app exchanges). So, while ISVs build software, they aren’t considered CSPs, and therefore cannot get their natively-built applications FedRAMP authorized. Instead, a natively-built CLM solution would be deployed within the client’s FedRAMP-authorized SaaS or PaaS environment – for example, within your Microsoft Azure Government or Salesforce Government Cloud – where the CLM solution then inherits many security controls and policies from the environment in which it’s deployed.
For further reading on FedRAMP’s applicability to ISVs, I recommend this excellent article by cybersecurity experts, Coalfire.
Evaluating SaaS vs. natively-built CLM applications for FedRAMP compliance looks different
With the distinction above in mind, let’s take a look at how you should evaluate each CLM solution type for FedRAMP compliance:
SaaS-based CLMs – As discussed above, CLM vendors in this category fall under FedRAMP’s definition of a CSP, so you’ll want to ensure they’ve secured FedRAMP authorization (not just FedRAMP “readiness”) for the specific product you are considering so that your organization can satisfy its compliance obligations. Use the FedRAMP Marketplace to confirm a CLM’s current authorization status, as well as its impact level for securing data (more on this topic in consideration #3 below).
Natively-Built CLMs – While natively-built cloud applications inherit many security controls and policies from the FedRAMP-authorized environment in which they’re deployed, this doesn’t mean these CLM vendors are in the clear. There are a variety of controls that are still the ISV’s responsibility, so it’s crucial to identify an experienced partner with information security and configuration best practices expertise. Based on our experience, any natively-built CLM vendor you consider should be able to demonstrate their compliance with the controls seen in the table below. In addition, an ISV will typically undergo routine independent assessments of its security controls, which are performed by the CSP (i.e., Microsoft, Salesforce, etc.) that holds the FedRAMP authorization for the environment in which the CLM solution is deployed. Successful participation in the CSP’s security assessments, along with remediation of any vulnerabilities found, should be demonstrated to you by any potential vendor in the natively-built CLM category.
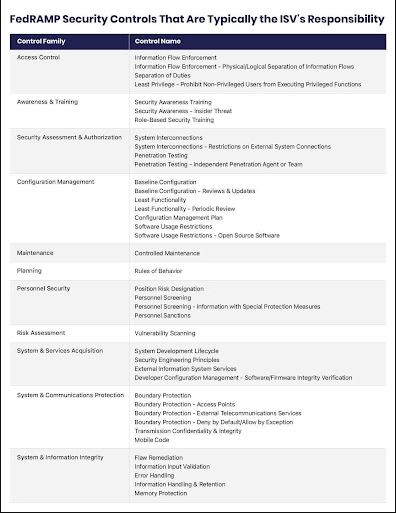
Figure 1 – FedRAMP Security Controls That Are Typically the ISV’s Responsibility
Your CLM’s FedRAMP impact level matters, now and in the future
Another important consideration when evaluating CLM solutions is the CSP’s security categorization of Low, Moderate, or High impact level. As part of FedRAMP authorization, a CSP must identify the types of data managed in its system and map this to the National Institute of Standards and Technology (NIST) standards and guidelines for securing data found in FIPS PUB 199 (see Figure 2 below).
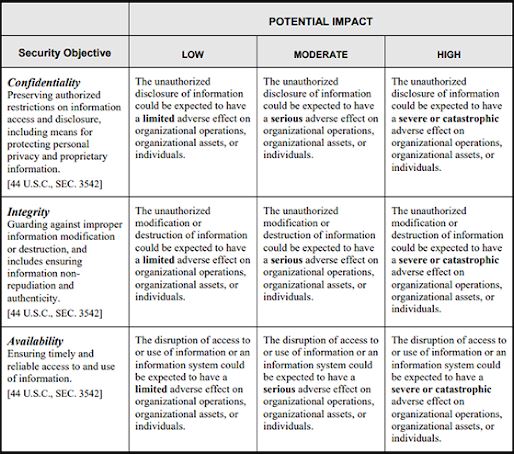
Figure 2 – NIST Standards & Guidelines for Securing Data
As this chart shows, there are three FedRAMP impact levels based on the security objectives of confidentiality, integrity, and availability. The higher the impact level, the greater the number of controls required of the CSP to secure and protect the data in its system.
So which FedRAMP impact level should you require of your CLM vendor? Answering this question necessitates an understanding of the obligations contained in your government contracts, as well as conversations with your CIO, General Counsel/Chief Compliance Officer, and other C-suite members.
Be sure to keep an eye toward the future. Might your current customers heighten their security requirements? Do you plan (or aspire) to broaden your reach into additional offices or agencies that may have more stringent requirements? Seek a CLM vendor now that enables, not limits, your future growth potential, which may necessitate choosing a FedRAMP High partner.
For CLM vendors that fall into the SaaS deployment model, you can verify their specific product’s designated impact level on the FedRAMP Marketplace. Similarly, for a natively-built CLM application, you can use the FedRAMP Marketplace to understand the impact level(s) associated with the platform(s) on which their software is deployed (e.g., Salesforce Government Cloud Plus, Microsoft Azure Government).
Summing it Up: FedRAMP and Other Considerations for a Potential CLM Partner
To sum things up, as a contracts professional who may be responsible for researching and assessing new tools and technologies for your department – such as CLM software – it’s imperative to have a working knowledge of FedRAMP considerations. Here are some critical questions to ask that will help you both assess a potential CLM vendor from a FedRAMP compliance perspective, as well as evaluate their solution’s ability to support you in successfully managing and navigating the unique complexities of the government contract lifecycle:
How is the vendor’s CLM system architected and deployed – is it SaaS or a natively-built application?
If SaaS, is the specific CLM product you’re considering FedRAMP authorized? Verify via the FedRAMP Marketplace.
If a natively-built application, what information security and configuration best practices expertise does the vendor bring to the table with regard to security controls owned by the ISV (see Figure 1 above)? Can the ISV demonstrate ongoing compliance with security assessments performed by the underlying platform’s CSP that holds FedRAMP authorization?
Which FedRAMP impact level(s) is/are supported by the vendor – Low, Moderate, and/or High? Verify via the FedRAMP Marketplace. How does this align to my organization’s current compliance obligations, as well as future growth plans?
Does the vendor’s system meet all other government security requirements (e.g., support CMMC compliance)?
Is the vendor’s system a commercially-oriented CLM being retrofitted for government contracting? Or is it purpose-built for our industry?
What specific features/capabilities are offered to support unique government contracting needs (e.g., automated clause library administration based on acquisition.gov)?
How much R&D investment is specifically made in the vendor’s CLM functionality? Is this investment stagnated or diluted across a broad product portfolio/products targeted to other industries?
Does the vendor offer a subscription-based model that includes ongoing, regular product updates to ensure your CLM system will evolve to support emerging market needs and industry best practices?
What capabilities are on the vendor’s product roadmap? When will they be released and how will these capabilities help you better do your job?
How up-to-date is the vendor’s user interface and user experience? What, if any, plans exist to refresh it?
You can apply for consideration to become a part of Executive Mosaic’s most exciting program. Contact us today to learn more about becoming a GovCon Expert and visit GovConWire.com to read the latest features on our industry.